The standard implementation of PGP encryption for Mac users is GPGTools, which is a suite of software that offers encryption for all areas of your Mac system. Pros: GPGTools integrates well with Apple Mail, as in the example above. Mac OS X Locate and double-click the downloaded image to mount it and then double-click the GoAnywhere Open PGP Studio installer. In the Welcome screen, click Next. Mac OS X Installation Welcome - GoAnywhere Open PGP Studio In the License Agreement screen, read and accept the License Agreement,. A project to bring GnuPG to Mac OS X with a nice front end and inter application services. Mac GNU Privacy Guard. I gladly may announce that a new and more active group has taken over the projects.
Pretty Good Privacy (PGP) is an encryption system used for both sending encrypted emails and encrypting sensitive files. Since its invention back in 1991, PGP has become the de facto standard for email security.
The popularity of PGP is based on two factors. The first is that the system was originally available as freeware, and so spread rapidly among users who wanted an extra level of security for their email messages. The second is that since PGP uses both symmetric encryption and public-key encryption, it allows users who have never met to send encrypted messages to each other without exchanging private encryption keys.
Get the Free Pen Testing Active Directory Environments EBook
If you want to improve the security of your email messages, PGP offers a relatively easy and cost-effective way to do this. In this guide, we’ll show you how.
How Does PGP Encryption Work?
PGP shares some features with other encryption systems you may have heard of, like Kerberos encryption (which is used to authenticate network users) and SSL encryption (which is used to secure websites).
At a basic level, PGP encryption uses a combination of two forms of encryption: symmetric key encryption, and public-key encryption.
In order to understand how PGP works, it’s useful to look at a diagram:
The mathematics behind encryption can get pretty complex (though you can take a look at the math if you like), so here we’ll stick to the basic concepts. At the highest level, this is how PGP encryption works:
- First, PGP generates a random session key using one of two (main) algorithms. This key is a huge number that cannot be guessed, and is only used once.
- Next, this session key is encrypted. This is done using the public key of the intended recipient of the message. The public key is tied to a particular person’s identity, and anyone can use it to send them a message.
- The sender sends their encrypted PGP session key to the recipient, and they are able to decrypt it using their private key. Using this session key, the recipient is now able to decrypt the actual message.
This might seem like a strange way to do things. Why would we encrypt the encryption key itself?
Well, the answer is pretty simple. Public key cryptography is much, much slower than symmetric encryption (where both the sender and recipient have the same key). Using symmetric encryption requires, though, that a sender share the encryption key with the recipient in plain text, and this would be insecure. So by encrypting the symmetric key using the (asymmetric) public-key system, PGP combines the efficiency of symmetric encryption with the security of public-key cryptography.
Example of PGP Encryption in Action
In practice, sending a message encrypted with PGP is simpler than the above explanation makes it sound. Let’s take a look at ProtonMail – as an example.
ProtonMail natively supports PGP, and all you have to do to encrypt your email is to select Sign Mail. You will see a padlock icon on the subject line of their emails. The email will look like this (the email addresses have been blurred for privacy reasons):
ProtonMail – like most email clients that offer PGP – hides all of the complexity of the encryption and decryption of the message. If you are communicating to users outside of ProtonMail, you need to send them your public key first.
And so, although the message was sent securely, the recipient does not have to worry about the complexities of how this was done.
PGP Encryption Uses
There are, essentially, three main uses of PGP:
- Sending and receiving encrypted emails.
- Verifying the identity of the person who has sent you this message.
- Encrypting files stored on your devices or in the cloud.
Of these three uses, the first – sending secure email – is by far the dominant application of PGP. But let’s take a brief look at all three
Encrypting Emails
As in the example above, most people use PGP to send encrypted emails. In the early years of PGP, it was mainly used by activists, journalists, and other people who deal with sensitive information. The PGP system was originally designed, in fact, by a peace and political activist named Paul Zimmerman, who recently joined Startpage, one of the most popular private search engines.
Today, the popularity of PGP has grown significantly. As more users have realized just how much information corporations and their governments are collecting on them, huge numbers of people now use the standard to keep their private information private.
Digital Signature Verification
A related use of PGP is that it can be used for email verification. If a journalist is unsure about the identity of a person sending them a message, for instance, they can use a Digital Signature alongside PGP to verify this.
Digital signatures work by using an algorithm to combine the sender’s key with the data they are sending. This generates a “hash function,” another algorithm that can convert a message to a block of data of fixed size. This is then encrypted using the sender’s private key.
The recipient of the message can then decrypt this data using the sender’s public key. If even one character of the message has been changed in transit, the recipient will know. This can indicate either the sender is not who they say they are, that they have tried to fake a Digital Signature, or that the message has been tampered with.
Encrypting Files
A third use of PGP is to encrypt files. Because the algorithm used by PGP – normally the RSA algorithm – is essentially unbreakable, PGP offers a highly secure way of encrypting files at rest, especially when used alongside a Threat Detection and Response Solution. In fact, this algorithm is so secure that it has even been used in high-profile malware such as the CryptoLocker malware.
Back in 2010, Symantec acquired PGP Corp., which held the rights for the PGP system. Since then, Symantec has become the dominant vendor of PGP file-encryption software through such products as Symantec Encryption Desktop and Symantec Encryption Desktop Storage. This software offers PGP encryption for all your files, whilst also hiding the complexities of encryption and decryption processes.
Do I Need Pretty Good Privacy Encryption?
Whether you need to use PGP encryption will depend on how secure you want your communications (or files) to be. As with any privacy or security software, using PGP requires that you do a little more work when sending and receiving messages, but can also dramatically improve the resilience of your systems to attack.
Let’s take a closer look.
Pros of PGP Encryption
The major pro of PGP encryption is that it is essentially unbreakable. That’s why it is still used by journalists and activists, and why it is often regarded as the best way of improving cloud security. In short, it is essentially impossible for anyone – be they a hacker or even the NSA – to break PGP encryption.
Though there have been some news stories that point out security flaws in some implementations of PGP, such as the Efail vulnerability, it’s important to recognize that PGP itself is still very secure.
Cons of PGP Encryption
The biggest con of PGP encryption is that it is not that user-friendly. This is changing – thanks to off-the-shelf solutions that we will come to shortly – but using PGP can add significant extra work and time to your daily schedule. In addition, those using the system need to be aware of how it works, in case they introduce security holes by using it incorrectly. This means that businesses considering a move to PGP will need to provide training.
For that reason, many businesses might want to consider alternatives. There are encrypted messaging apps like Signal, for instance, that offer encryption that is more straightforward to use. In terms of storing data, anonymisation can be a good alternative to encryption and can be a more efficient use of resources.
Finally, you should be aware that PGP encrypts your messages, but it doesn’t make you anonymous. Unlike anonymous browsers using proxy servers or working through a VPN to hide your true location, emails sent through PGP can be traced to a sender and recipient. Their subject lines are not encrypted either, so you shouldn’t put any sensitive information there.
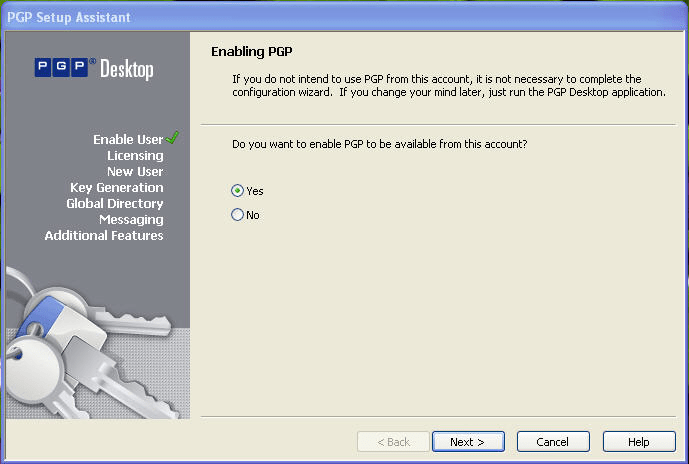
How Do I Set Up PGP Encryption?
In the vast majority of cases, setting up PGP encryption involves downloading an add-on for your email program, and then following the installation instructions. There are add-ons like this available for Thunderbird, Outlook, and Apple Mail, and we will describe these below. In recent years we have also seen the emergence of a number of online email systems that include PGP by default (the most famous being ProtonMail).
For those of you looking to use PGP to encrypt your files, there are a number of large-scale software solutions available. Symantec, for example, offers PGP-based products such as Symantec File Share Encryption for encrypting files shared across a network and Symantec Endpoint Encryption for full disk encryption on desktops, mobile devices and removable storage.
PGP Encryption Software
If you are looking to start using PGP encryption, this will normally involve downloading a piece of software that automates the process of encryption and decryption. There are a number of different products available to do this, but you should be aware of what to look for.
How to Select PGP Software
- Your primary reason for using PGP is to ensure the security of your messages. When looking for PGP software, therefore, security should be your first concern. Though PGP itself is unbreakable, there have been instances where specific implementations have been compromised. Unless you are an experienced coder, spotting these vulnerabilities is essentially impossible, and so the best solution is to check for any reported vulnerabilities in the software you are considering.
- Beyond this, choosing PGP software comes down to your personal (or business) needs. It’s unlikely, for instance, that you need to encrypt every email you send, and so downloading an add-on for your day-to-day email client might be overkill. Instead, consider using an online PGP service to send important emails.
- Finally, choose a software provider who also provides dedicated support, either through a customer support team or a user community. Learning to use PGP can often come with frustrations as you first navigate the system, and you’re likely to need help at this stage.
Different PGP Solutions
Depending on why you are using PGP, and how often you need to use it, there are several different approaches to setting it up. In this section we will focus on what most users will need from PGP – secure email – rather than encrypted file storage, which is a more complex issue. Here, then, are five solutions for implementing PGP on your home or business networks.
1. Outlook with gpg4o
Gpg4o is one of the most popular PGP solutions for Windows users and aims to integrate seamlessly with Outlook 2010 – 2016.
- Pros: Gpg4o offers simple handling for emails, and integrates well with Outlook. For most Windows users, it offers the easiest and most user-friendly PGP add-on out there.
- Cons: Though Gpg4o is built around the OpenPGP standard, which is open-source and available for scrutiny, the add-on itself is proprietary. In addition, a business license for the add-on is relatively expensive at €56.36, though for this price you also get dedicated support.
2. Apple Mail With GPGTools
The standard implementation of PGP encryption for Mac users is GPGTools, which is a suite of software that offers encryption for all areas of your Mac system.
- Pros: GPGTools integrates well with Apple Mail, as in the example above. It also offers a key manager, software that allows you to use PGP in almost any application, and a tool that allows you to use the command line for the most common key management tasks.
- Cons: Though GPGTools offers the easiest way for Mac users to start using PGP encryption, using this encryption for your primary email can slow the performance of Apple Mail.
3. Thunderbird With Enigmail
As with the tools above, Enigmail was designed to integrate with a specific email client, in this case, Thunderbird.
- Pros: Enigmail has a few key advantages. The first is that, like Thunderbird, the add-on is platform-independent. Secondly, the add-on is completely open-source and is provided for free. It is also regularly updated, and the development team is quick to respond to identified instances of malware.
- Cons: As with most open-source software, Enigmail doesn’t provide dedicated support. On the other hand, the user community is large and active and has compiled a huge amount of reference materials to help you get started.
4. ProtonMail
ProtonMail was one of the first secure email providers and remains one of the most popular. Unlike the solutions above, ProtonMail operates through a web portal, meaning that it is easily separable from your everyday inbox.
Pgp Machine Learning
- Pros: ProtonMail automatically uses PGP encryption for messages sent between two users of its service, which takes most of the complexity out of setting up and using PGP. Services like this – Hushmail and Mailfence are similar – and are an easy way of sending the occasional encrypted email without re-setting your entire system.
- Cons: Because ProtonMail implements PGP through JavaScript embedded in a website, some people don’t regard it as completely secure. That said, ProtonMail takes the security of their system very seriously, and have been extremely active in improving it.
5. Android and FairEmail

Lastly is FairEmail, which extends PGP encryption to Android phones. This is a stand-alone email app that is free to use.
- Pros: FairEmail is the simplest solution around for users who want to use PGP encryption on their Android phone. It gives you the option of encrypting messages, rather than doing this by default, so you can choose what to encrypt.
- Cons: Because usage of PGP through Android is still quite rare, the user community for FairEmail is quite small.
Pretty Good Privacy FAQ
Even after the explanation above, you may still have some questions. Here are the answers to the most commonly asked questions about PGP.
Q: Is PGP encryption secure?
A: Yes. Though PGP is now more than 20 years old, there have been no vulnerabilities found in the basic implementation of the system. That said, encrypting your emails is not sufficient for total security, and you should always use PGP in combination with a full cybersecurity suite that includes threat detection software.
Q: How does PGP encryption work?
A: PGP uses a combination of symmetric and public-key cryptography to provide users with a secure way to send messages to each other.
Q: What is the best PGP software?
A: The “best” PGP software will depend on your needs. Most people don’t need to encrypt all of their emails, and so for most people a web-based PGP email provider will be the best solution. That said, if you are frequently sending emails that need to be encrypted, you can consider downloading a PGP add-on for your standard email client.
Q: Do I need encryption software?
A: It depends. If you are storing customer information, the answer is yes. Encrypting your personal files is not a necessity, but can dramatically improve your defenses against a cyberattack. Encryption software based on PGP is generally some of the easiest to work with, and is a good place to start when it comes to encrypting your files.
PGP encryption can be a powerful tool in protecting your data, your privacy, and your security. It provides you with a relatively easy, completely secure method of sending emails, and also allows you to verify the identity of the people you are communicating with. Because PGP add-ons are also available for most major email clients, this form of encryption is generally easy to implement.
All this said, secure email is only one aspect of cybersecurity. You should ensure that, in addition to PGP, you also use a robust data security platform and Data Loss Prevention software. Making use of as wide a range of tools as possible is the best way to ensure your privacy and security.
- Installing Software
- Generating GPG keys
- Using your newly created GPG key with Cerb
- Publishing your public key
To automatically decrypt a received encrypted message in Cerb, you need to have the corresponding private key in your keyring. If you receive an encrypted message that can’t be decrypted, Cerb will leave the encrypted content as an attachment on the message that you can decrypt offline. This is the most secure option, but the content of the message won’t be readable or searchable within Cerb.
If you want automatic decryption of messages, you need to consider the security implications of leaving your private key on the server. At the minimum, we recommend that you create a subkey following the steps documented here so you won’t be storing your master key on the server.
If you are running Linux or Windows, the instructions below can be used with some modifications. We will release platform specific guides for them in the future.
Install Homebrew
This guide assumes you use Homebrew to install packages on your Mac. If that isn’t the case, Homebrew is a package manager (similar to RPM or deb on Linux) that makesit easy to install software on your Mac. Please visit http://brew.sh and follow the instructions to install it.
Install GPG
To generate your keys, you need to install GnuPG (aka GPG). GPG is a free software alternative to the closed source commercial PGP. To install GPG with Homebrew, it’s as simple as:
Enable GUI for passphrase entry
You might have noticed we installed two things, GPG and something called pinentry-mac. Pinentry-mac is a tool which prompts with a native dialog box for your GPG key passphrase and alsoallows you to store the password in your Mac’s Keychain. As Homebrew helpfully prompted after installing pinentry-mac, we now need to enable it.
While pinentry-mac allows you to save your passphrase, in the interest of security you shouldn't.
To enable it, you first need to run GPG to have it setup its directory structure.
This can be accomplished by simply running:
You don’t have any keys in your keyring yet. Let’s fix that in a moment. After getting GPG to create its directory structure, we now need to enable pinentry-mac.We do this by editing the file $HOME/.gnupg/gpg-agent.conf. You can use VIM (or a text editor of your choice) as shown below:
Or you can accomplish the same thing by running this:
After setting pinentry-mac up, when GPG prompts you for a passphrase, you’ll see something like this:
Now that you have GPG installed, we need to generate the keys which are used for encrypted email. Following best practices, we will be generating a master key and then a subkey for usage by Cerb.This way if your subkey is ever compromised, it’s a simple process to revoke and replace it. The master key you should protect as you would your bank password.
Generate master key
We will be removing the Sign and Encrypt capabilities from the master key forcing usage of subkeys for those operations. This limits the damage that can be done if the master key is ever compromised.
To generate the master key, follow these steps:
- To start the process:
- When prompted for what kind of key, pick option:
(8) RSA (set your own capabilities). - Next you want to toggle off the sign and encrypt capabilities from the key.
- When prompted for capabilities, type
sand hit enter to toggle off the Sign capability. - Next type
eand hit enter to toggle off the Encrypt capability. - Confirm that the current allowed actions only lists
Certify, then typeqand hit enter to finish setting capabilities.
- When prompted for capabilities, type
- Now you are prompted for how long the RSA key should be. Type
4096to set the highest security that GPG currently supports. - For expiration, we suggest picking
0so the key doesn’t expire. - Now GPG needs to know who this key is for. For the Real Name, we suggest picking the same “friendly name” you use for outgoing email from Cerb.
- Next provide the email address you want to use for receiving encrypted email.
- We will reference this email as
YOUR@EMAIL.comfor the remainder of this guide.
- We will reference this email as
- If you’d like to enter a comment for the key, you can do so next. Otherwise hit enter to skip it.
- If everything looks good at this point, hit
ofor Okay. - You will now be prompted for your master key passphrase. Please ensure this is a secure password that you have not used anywhere else.
If you are unsure about any of the above, the screenshot below shows the entire key creation process.
Set secure preferences on key
Now that your master key is created, we want to set the preferences on the key to ensure current best practices.
- To edit the key, you need to run:
- Paste in the following to set the preferences:
- Type
yto confirm. - Type
saveto save and exit.
Add GPG subkey for Cerb
Pgp Mac Tutorial
Now that you have your master key, we need to create the subkey used for Encrypt and Sign in Cerb. The process for this is similar to what you have already done before.
- To add the subkey, you need to first run:
- At the prompt, type
addkey. - Choose option:
(8) RSA (set your own capabilities)as before. - Unlike before, the capabilities are already set the way we want (“Sign Encrypt”), so type
qto finish capability selection. - Type
4096as previously done for the keysize. - Next, we suggest using
0for no expiration as before. - Confirm
yat the next two prompts. - After entering your passphrase, your subkey is now created.
- Type
saveto quit and exit.
Export keys for safe storage
This step is critical to the safety of your GPG keys. If you don't do this, your keys could be forever lost or worse.
To export your private key, run the following replacing YOUR@EMAIL.com in both places with your email address used when creating the key.
We will also export the public key to keep with the private key:
Next, we will create a revocation certificate for the key in case it is ever compromised:
Follow the prompts to create the revocation certificate. For reason, we suggest 1 = Key has been compromised and you can hit enter on the description line (it’s not needed).
Now that we have these three files created, back them up on a USB drive and put in a very safe place (safety deposit box is a common suggestion).After copying them to a USB drive, we highly recommend deleting the file ending in .private.gpg-key and .gpg-revocation-certificate immediately.You do not need to delete the file ending in .public.gpg-key as we will use it later.
Remove passphrase for using with Cerb
Now that the master key is preserved safely, we need to remove the passphrase for using your GPG key with Cerb.This isn’t a standard process, so GPG is persistent in making sure it’s what you really want to do.
- Edit the key as before via:
- At the prompt, type
passwd. - You will first be prompted for your existing passphrase.
- When prompted for a new passphrase, hit enter.
- When prompted, pick “Yes, protection is not needed”.
- The above two steps repeat multiple times, keep repeating until they stop asking.
- Type
quitat the prompt to finish.
The screenshots below illustrate the process and the prompts you must acknowledge.
Delete master key from local keyring
Now that your GPG keys are backed up and currently not secured by a password, we need to delete the master key locally for security reasons.
- First we need to get the keygrip for the master key so we know what to delete:
- Take note of the first
Keygrip =line in the output, consult the below screenshot as needed.- Now that you have the key grip, you need to use it to delete the master key locally from your keyring:
- Finally we want to make sure it’s really gone:
As shown in the below screenshot, make sure that there is a # after sec at the beginning of the 3rd line. This indicates that the master key is offline as it should be.
Export subkey for using with Cerb
With all that out of the way, we need to export the subkey we created to use it with Cerb. Run this in a Terminal to export the subkey:
You will use the contents of this file to enable Cerb to decrypt encrypted email sent to it in the next step.
There are two methods for importing your subkey into Cerb. We recommend importing it via your browser for simplicity.
Importing via your browser
Cerb 8.1.0 doesn’t have a direct way to add GPG private keys, but thankfully GPG treats them the same for purposes of importing.
- Navigate to Search » Public Keys.
- Add a new record by clicking on the (+) above the worklist.
Pgp Mac Mail
- For the name, enter in
YOUR@EMAIL.com private subkeyor similar. - Paste in the contents of the exported private subkey as generated previously.
Skip over the next step and jump ahead to Publishing your public key.
Importing via command line
To import via command line, you first need to connect via SSH to the server where Cerb is hosted. If you are a Cerb Cloud customer,this isn’t possible so you will need to use the above instructions to do it via your browser.
- Change into the directory where you have Cerb installed.
- Tell GPG where to find the keystore used by Cerb:
- Check to see if you have existing private keys:
- Import the subkey you created previously:
- Verify the key exists now and that the master key is offline as before:
Now that you have Cerb setup to receive encrypted email, you need to tell the world about your public key so they can encrypt emails to you.There are a number of different public key servers commonly used, so we recommend submitting to them all for coverage.
You’ll need your public key to do this, so if you don’t still have it from the Export keys for safe storage step earlier, you can re-export it now with:
Using Keybase
We highly recommend using a service like Keybase, which not only verifies the email address of a public key, but also allows the key ownerto prove their identity by verifying ownership of domain names, profiles on various services (e.g. Twitter, GitHub), Bitcoin wallets, etc.
As the setup is a bit more involved than the below three options and subject to change, we recommend visitinghttps://keybase.io/ and following their guide.
You can also import public keys from Keybase right into Cerb.
Using MIT’s public key server
MIT’s public key server is accessible at https://pgp.mit.edu. The screenshot below shows where to submit your public key:
Free Pgp For Mac
Using Symantec’s public key server
Pgp Mac Outlook
Symantec’s public key server is accessible at https://keyserver.pgp.com.
To submit a key to them, visit the Submit Key page and upload your key there as shown in the screenshot below.
Using Key-server.io’s public key server
Key-server.io’s public key server is accessible at http://pgp.key-server.io. The screenshot below shows where to submit your public key:
Links on how to setup setup storage of your private key on a popular hardware device: